Satori Perspectives: BADBOX 2.0 Ups the Sophistication with a New Reverse Engineering Challenge
Read time: 5 minutesLindsay Kaye

In 2023, The HUMAN Satori Threat Intelligence published a report on a campaign called BADBOX and the corresponding ad fraud component, PEACHPIT. We successfully disrupted the advertising fraud component and our report led to industry-wide action, including a letter from the EFF to the FTC asking them to address the resale of these malware-laden Android TV set-top boxes. Now, BADBOX is back, and it’s bigger, badder, and more sophisticated than ever. And thanks to our partners, especially Google and ShadowServer, we’ve made huge strides in disrupting it.
How BADBOX Evolved from 74,000 to 1,000,000 Backdoored Devices
During the first BADBOX campaign, we observed around 74,000 devices that we believed were BADBOXes; these devices were infected with a known backdoor malware called Triada by threat actors of Chinese origin. These backdoors communicated with a command and control server (C2) to download additional functionality in the form of “modules”, one of which included the ad fraud module we named PEACHPIT. At its peak, PEACHPIT generated 9 billion fraudulent bid requests per day from 280,000 devices. After HUMAN implemented markers to block the fraudulent traffic, the threat actor group abandoned this part of the fraud scheme.
In comes BADBOX 2.0: HUMAN continued to track the actor group via a technical anomaly in their network traffic, which revealed that the group was in the middle of reconstructing their campaign with even more sophistication than the first. We found that they had created an entire fraudulent ecosystem, including over 200 backdoors, an unofficial app marketplace hosting rebundled and infected applications, and four types of fraud modules. These fraud modules included hidden webview ad fraud, hidden ads, click fraud, and proxyjacking. You can read our report here. We saw over 1 million backdoored devices with BADBOX 2.0—a huge increase over the 74,000 from the earlier campaign. Like I said, bigger and badder.
Inside the BADBOX 2.0 Investigation: Backdoors, Encryption, and Infrastructure Analysis
One of the most interesting parts of this investigation was seeing the increased sophistication of the campaign as compared with the first BADBOX. That was evident in the development of the “fraud ecosystem,” as well as the addition of new fraud schemes we hadn’t seen in BADBOX.
This time, the backdoor itself presented some added reverse engineering challenges, including encrypting a second stage using the XXTEA algorithm. XXTEA is a block cipher, and at least in my experience, it’s fairly uncommon to see in malware. More often, I see RC4 and AES256, or some kind of custom XOR-based cipher in most of the samples I look at, so this was an unusual but fun challenge. Generally, a good way to recognize XXTEA is via the DELTA value 0x9e3779b9 in combination with the piece of the algorithm I have highlighted in the screenshot below. You might notice that instead of 0x9e3779b9, the Ghidra screenshot shows -0x61c88647. This is because Ghidra is interpreting the value as a signed integer, not an unsigned integer – the value is still the DELTA we expect.
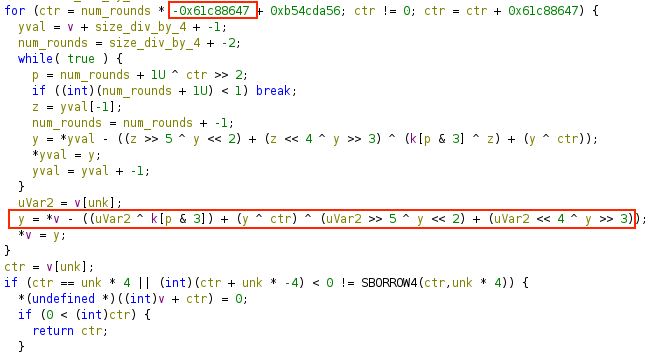
As some other researchers have pointed out, the XXTEA algorithm is a modified version, so out-of-the-box decryption code won’t work. In order to extract the next stage, I ended up having to implement my own 🙂.
Ultimately, one of the most amazing parts of this investigation was what a full team effort it was and how Satori’s broad skillsets came into play. Our team has great expertise in finding and disrupting ad fraud in the supply chain, Android and native code analysis, investigation into entities, and infrastructure analysis. This investigation required all of these, and the magnitude of what we’ve uncovered demonstrates this. Our findings from research like BADBOX 2.0 are incorporated into our products to protect our customers from the threats we identify.
What’s Next: Ongoing Threat Monitoring and Disruption Efforts
The battle against the BADBOX 2.0 threat actors isn’t over yet, and the threat remains ongoing. At HUMAN, we continue to monitor for new apps, IOCs, and other artifacts from this threat actor group, as well as work in collaboration with our partners and law enforcement to disrupt the threat. Currently, we are protecting customers from ad fraud campaigns as well as attacks perpetrated via the residential proxy network, such as ATO, scalping, scraping, and fake account creation. Again, a profuse thanks to Google, Trend Micro, ShadowServer, and our other partners for the joint effort to take on this campaign and a very persistent threat actor group. Stay tuned for some more on our disruption efforts!
For more information on BADBOX 2.0, check out our overview blog and the full technical breakdown of our investigation and disruption efforts.
Or attend our upcoming webinar to discuss the threat intel behind the BADBOX 2.0 disruption with the Satori team:

More Satori Perspectives:
Examining Threat Activity During the Super Bowl
Cybercriminals Just Lost Some of Their Most Popular Forums—Will it Actually Slow Them Down?